I work in IT security. Cryptography is not abstract to me — it is the practical foundation of almost everything I do professionally. So when the “quantum computing will kill Bitcoin” conversation comes up, I pay attention differently than most people writing about it.
The honest answer is that the threat is real, the timeline is genuinely uncertain, and most of the coverage dramatically misrepresents where the technology actually stands. Here is the clearer version.
What Bitcoin’s Security Actually Rests On
Bitcoin uses two cryptographic systems that are relevant here. The first is SHA-256, which secures the proof-of-work mining process. The second — and more vulnerable one — is the Elliptic Curve Digital Signature Algorithm (ECDSA), which secures wallet ownership and transaction signing.
ECDSA works on a mathematical principle called the elliptic curve discrete logarithm problem. In simple terms: given a public key, deriving the corresponding private key requires solving a mathematical problem that is computationally infeasible for classical computers. The numbers involved are large enough that even the most powerful supercomputers today could not brute-force the calculation in any practical timeframe.
Quantum computers change this calculus because of an algorithm called Shor’s Algorithm, published by mathematician Peter Shor in 1994. Shor’s Algorithm can solve the discrete logarithm problem exponentially faster than any classical approach. On a sufficiently powerful quantum computer, deriving a Bitcoin private key from a public key becomes a tractable problem rather than an intractable one.
That is the genuine threat. It is a real mathematical vulnerability, not speculation.
Where Quantum Computing Actually Stands in 2026
Here is where most coverage goes wrong: it describes the theoretical threat accurately, then dramatically overstates how close we are to it being practically realizable.
To run Shor’s Algorithm against Bitcoin’s 256-bit elliptic curve encryption, researchers estimate you need somewhere between 1,500 and 4,000 stable logical qubits — not physical qubits, logical qubits. The distinction is critical.
Physical qubits are what the hardware actually contains. They are noisy, error-prone, and require extensive error correction. Logical qubits are the error-corrected, stable units of computation that can actually run complex algorithms reliably. Converting physical qubits to logical qubits requires a large ratio — current estimates suggest you need somewhere between 1,000 and 10,000 physical qubits per logical qubit, depending on the architecture and error rate.
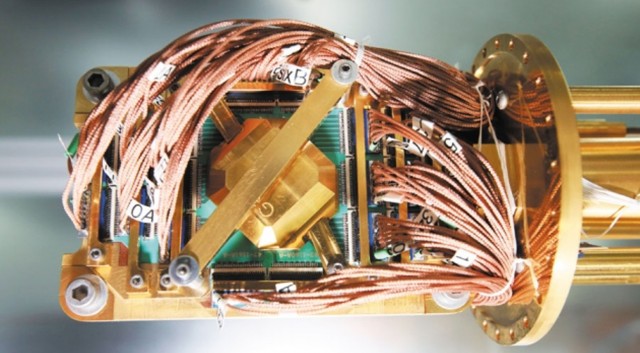
IBM’s Condor processor, announced in late 2023, has 1,121 physical qubits. Google’s Willow chip, announced in late 2024, demonstrated significant progress on error correction and represents genuine advancement in quantum hardware. But “significant progress on error correction” and “4,000 stable logical qubits capable of running Shor’s Algorithm against 256-bit encryption” are separated by an enormous engineering gap.
Most credible estimates from quantum computing researchers place the capability to break current Bitcoin encryption at somewhere between 2030 and 2040, with considerable uncertainty in both directions. Claims that it could happen within two or three years are not well-supported by the published research.
Which Bitcoin Addresses Are Actually Vulnerable
Not all Bitcoin addresses have equal exposure, and understanding the difference matters for anyone who holds crypto.
When you send Bitcoin, your transaction reveals your public key to the network. Addresses that have previously sent transactions have therefore exposed their public key — these are the addresses most vulnerable to a future quantum attack, because an attacker with sufficient quantum capability could derive the private key from the known public key.
Addresses that have only received funds and never sent them are meaningfully safer. Bitcoin’s address format involves hashing the public key (using SHA-256 and then RIPEMD-160), which provides an additional layer. Until a transaction is sent, the underlying public key is not directly visible on the blockchain. This does not make these addresses permanently safe — eventually any address that sends a transaction exposes its public key — but it does mean the exposure is not universal or immediate.
The addresses that security researchers flag as most at risk are the early Bitcoin holdings from 2009-2010, when the original pay-to-public-key (P2PK) format was used, which exposes the public key directly without hashing. This includes a large portion of the coins associated with Bitcoin’s earliest mining activity.
The Post-Quantum Cryptography Response
The Bitcoin development community and the broader cryptography world are not ignoring this. Post-quantum cryptography (PQC) has been an active research area for over a decade.
In 2024, NIST (the US National Institute of Standards and Technology) finalized its first set of post-quantum cryptographic standards, including algorithms based on lattice mathematics (specifically CRYSTALS-Kyber for key encapsulation and CRYSTALS-Dilithium for digital signatures). These algorithms are designed to be resistant to both classical and quantum attacks.
The practical question for Bitcoin is whether and how the network would upgrade to quantum-resistant cryptographic standards before quantum computers reach the capability to threaten existing encryption.
Bitcoin upgrades through a consensus mechanism — major changes require broad agreement among miners, node operators, and the broader development community. A migration to post-quantum signatures would be one of the most significant changes in Bitcoin’s history. It would likely require a soft fork, a coordinated migration period, and would need to address the genuine problem of what happens to coins in addresses that can no longer be accessed (lost keys, dormant wallets, coins belonging to deceased holders). There are estimated to be several million Bitcoin in addresses that cannot be practically migrated.
None of this is insurmountable, but it is also not simple. The coordination challenge is significant, and “Bitcoin will just upgrade” understates the complexity of actually executing that upgrade across a decentralized network.
The Geopolitical Dimension, Handled Carefully
Some coverage frames quantum computing as a geopolitical weapon — China develops quantum supremacy, drains Bitcoin wallets, crashes the dollar. This framing is more dramatic than useful.
What is accurate: national governments are investing heavily in quantum computing research, and the capability gaps between different countries’ programs are not fully transparent. China’s quantum research program is substantial and has produced significant published results. The US, through DARPA and private-sector investment, has also been a major driver of progress.
What is less accurate: the scenario where a state actor uses quantum capability to secretly drain Bitcoin wallets without the crypto community noticing is far less clean than the headlines suggest. A successful cryptographic attack against Bitcoin at scale would be detectable — anomalous transactions, unexpected movements from long-dormant addresses — and would likely trigger a market response that complicates the “silent attack” narrative.
The more realistic concern is not a dramatic heist but the slower erosion of confidence in Bitcoin’s security model as quantum hardware continues to advance and the timeline to cryptographic vulnerability becomes more credible.
What This Means Practically for Someone Holding Bitcoin
A few straightforward points:
If you are holding Bitcoin in addresses that have previously sent transactions, your public key is already exposed. This is not an immediate problem given current quantum hardware limitations, but it is worth understanding.
Best practice from a security standpoint: use addresses once, move funds to new addresses after sending. This is good hygiene regardless of quantum concerns — it also improves privacy.
Watch the NIST post-quantum standards adoption curve. When major exchanges, hardware wallet manufacturers, and other infrastructure providers begin implementing PQC standards, that will be a meaningful signal about the timeline the security community believes is relevant.
Do not make significant financial decisions based on dramatic “Q-Day is coming” narratives without checking the actual state of quantum hardware. The threat is real but the timeline is measured in years to a decade or more, not months.
The Honest Summary
Quantum computing represents a genuine long-term threat to Bitcoin’s current cryptographic foundation. Shor’s Algorithm, if run on a sufficiently powerful quantum computer, could derive private keys from public keys. The capability to do this against Bitcoin’s 256-bit ECDSA does not currently exist and is probably at minimum several years away.
The Bitcoin community is aware of the problem. Post-quantum cryptographic standards now exist and are being adopted in other contexts. Whether Bitcoin can execute the coordination required to migrate to quantum-resistant cryptography before quantum hardware reaches the relevant capability threshold is an open question — one that is worth tracking, not panicking about.
My professional read: the threat is real enough to monitor seriously, not imminent enough to warrant emergency action, and handled better by watching the actual engineering progress than by reading coverage that treats every quantum computing announcement as confirmation that Bitcoin is doomed.
Sources referenced:
- NIST Post-Quantum Cryptography Standards (FIPS 203, 204, 205) — finalized 2024
- IBM Quantum Roadmap and Condor processor documentation
- Google Quantum AI — Willow chip research paper (2024)
- Estimates on logical qubit requirements for Shor’s Algorithm: peer-reviewed papers in Physical Review Applied and Nature
- Bitcoin Improvement Proposals (BIPs) related to address format and migration
This article is for informational and educational purposes only. Nothing here constitutes financial or investment advice. Cryptocurrency investments carry significant risk.